Data Protection & Cybersecurity Services

At QLine IT, we understand that protecting company data is not just a legal requirement; it’s essential to maintaining client trust and safeguarding your business operations.
Our comprehensive approach covers every aspect of data security, from user access controls and hardware security to network configuration and company procedures, ensuring compliance with GDPR, the Data Protection Act, and Cyber Essentials standards.
Our services include:
Protecting Company Data
User Access Control
Hardware Security
Data Classification
Network Configuration
Company Procedures
Protecting Company Data
Protecting company data is a legal and ethical responsibility. Clients trust that their personal information will be handled securely, not sold, and not used for unsolicited marketing. Businesses rely on this data for essential functions such as order tracking, account management, and HR administration.
Regulations also impose strict retention rules. For example, financial records must be stored for several years for tax purposes, while health and social care records have their own statutory timelines. However, GDPR requires that personal data be retained only for as long as necessary for its intended purpose.
Under GDPR Article 5(1)(e), companies must review their data regularly, justify its retention, and securely delete or anonymise it when no longer needed—reducing legal risk and maintaining compliance.

User Access Control
Controlling who can access specific types of data is critical to security and compliance. Access should be granted only on the basis of operational need and role requirements.
We implement role-based access control (RBAC), ensuring staff can only access the data essential to their job. This layered permission structure helps prevent accidental data exposure and malicious activity.
We also carry out regular access reviews and permission updates to keep your systems secure, ensuring compliance with GDPR and Cyber Essentials access control requirements.
Hardware Security
Most company data is accessed via computers, laptops, or mobile devices. Configuring these devices securely is one of the most cost-effective ways to protect information. This includes enabling two-factor authentication (2FA), enforcing strong passwords or PIN codes, and applying user role restrictions.
We establish structured onboarding processes to define exactly what each user can access from day one, preventing unnecessary permissions and minimising security risks.
Physical security is equally important. We advise on secure storage, asset tracking, and theft prevention—key requirements under GDPR and Cyber Essentials.


Data Classification
Every organisation handles a variety of data types, from HR records to client databases. We classify data not just by department, but by its sensitivity and risk level.
Following GDPR and Cyber Essentials guidance, we ensure you know exactly what data you hold, where it is stored, who can access it, and how it is protected.
We use four main classification levels—Public, Internal, Confidential, and Restricted—with appropriate security controls applied to each, ensuring compliance and reducing breach risk.
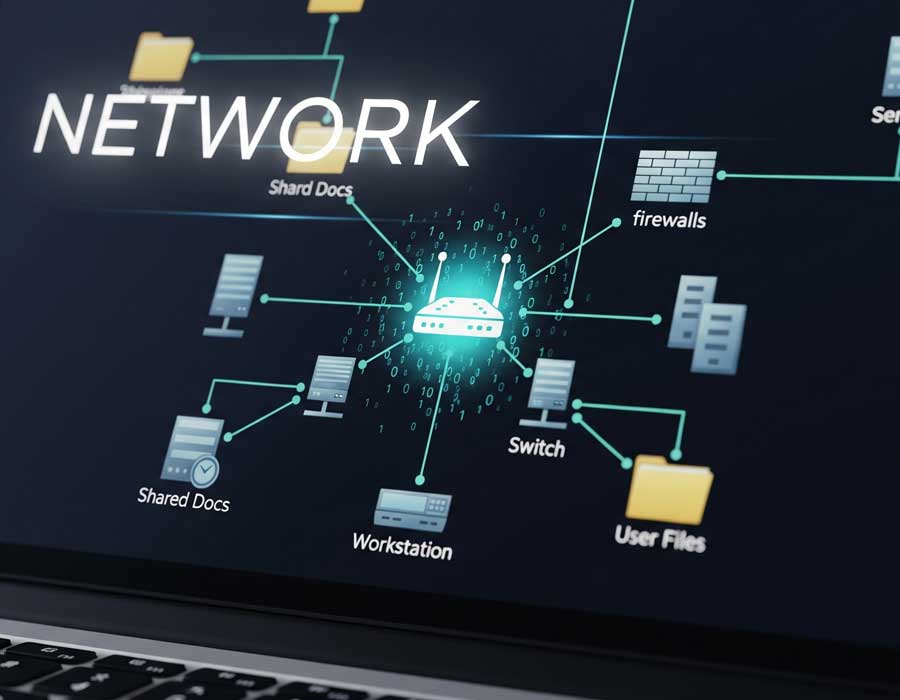
Network Configuration
A poorly configured network can undermine even the most secure applications. Whether your team works in the office or remotely, secure network setup is essential.
We assess vulnerabilities such as open ports, outdated firmware, and unsecured wireless access points, then implement solutions to protect your systems.
Cost-effective measures include segregating guest and internal Wi-Fi, deploying VLANs to isolate departments or device types, locking unused network ports, applying firmware updates, and enforcing WPA3-level authentication.
Company Procedures
Well-documented company procedures are one of the simplest and most effective ways to comply with GDPR and the Data Protection Act.
For example, an Onboarding & Access Authorisation Procedure ensures new employees are given only the permissions they require, reducing security risks and improving compliance.
We help businesses design procedures that improve consistency, support staff training, and create clear audit trails—without disrupting daily operations.
IT Solutions
Lets discuss how we can protect your company data and ensure compliance in this ever changing and challenging landscape.
We are experts in the field of Data Protection and Cybersecurity.
QLine IT has built its reputation as a trusted authority in Data Protection and Cybersecurity by delivering a holistic, standards-driven approach that goes beyond basic IT support. Based in Leeds and Cyber Essentials certified, we combine deep technical expertise with a strong understanding of legal and regulatory frameworks, ensuring our clients not only remain compliant with GDPR and the Data Protection Act, but also operate with optimal security practices that protect both data integrity and client trust.
Our expertise begins with a clear recognition that safeguarding data is both a legal obligation and a business necessity. We can help organisations meet GDPR’s strict requirements; such as the principle of storing personal data only for as long as necessary under Article 5(1)(e), while implementing secure deletion or anonymisation processes to reduce legal risks and maintain compliance. This regulatory knowledge is coupled with practical, technical safeguards that address every layer of data protection throughout our clients businesses.
Cyber Essentials Certified – independently verified security measures.
GDPR Compliance Expertise – aligning IT systems with legal requirements.
Custom Security Solutions – tailored to your business environment.
UK-Wide Coverage – supporting clients in Leeds and across the UK.
Case Study – Coming Soon…
